What is Network Protocol?A Protocol can be defined as rules governing the syntax, semantics and synchronization of communication.
In computing, A Protocol is a convention or standard that controls or enables the connection, communication and data transfer between two computing endpoints.
Protocols may be implemented by Hardware, Software or a Combination of two. At the lowest level, a protocol defines the behaviour of a hardware connection.
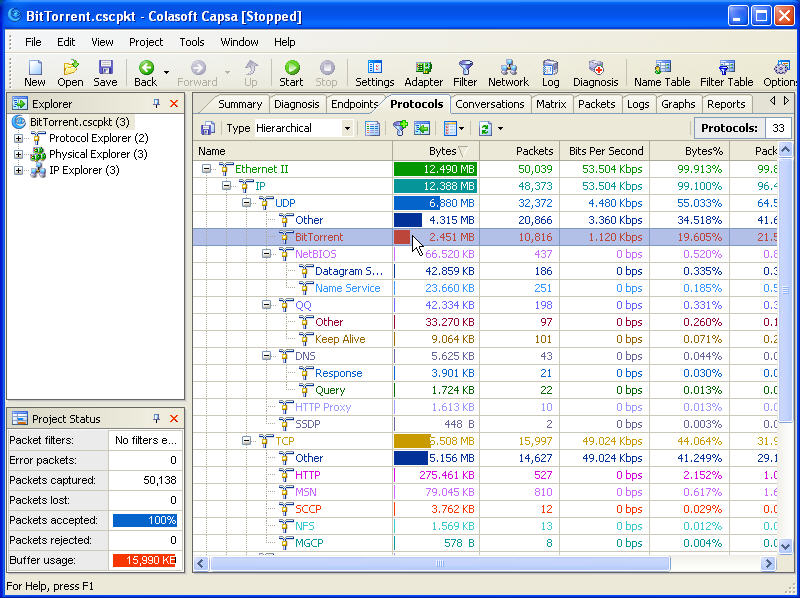
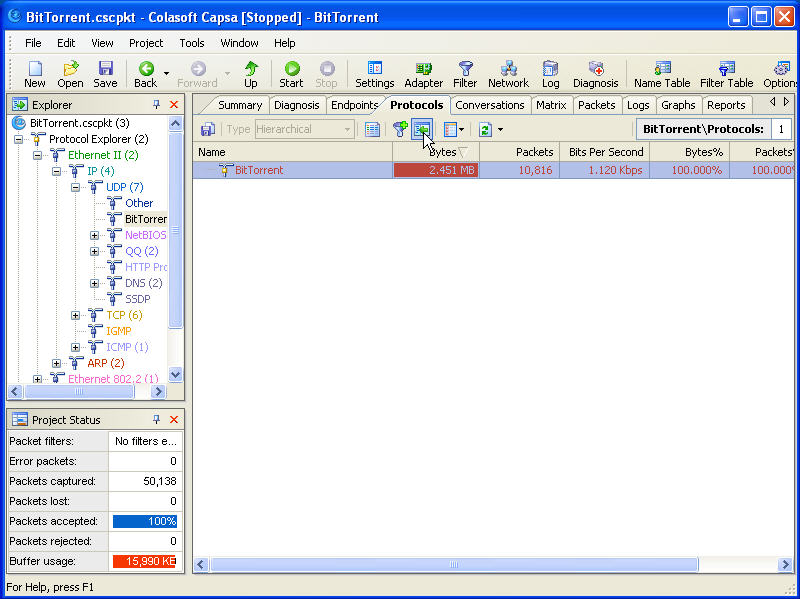
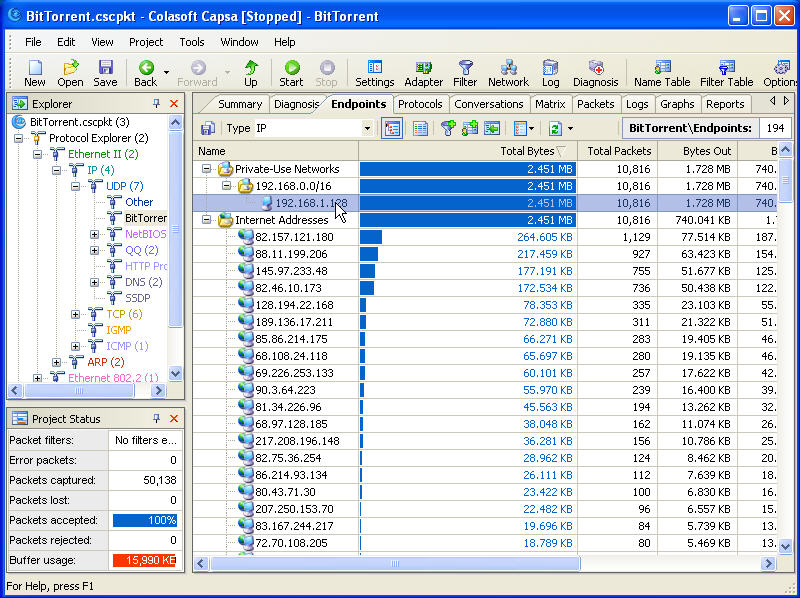
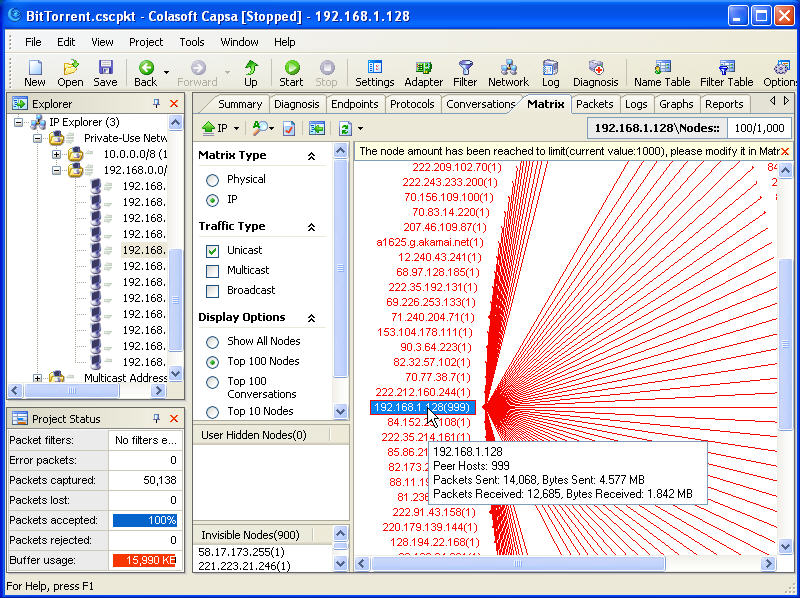
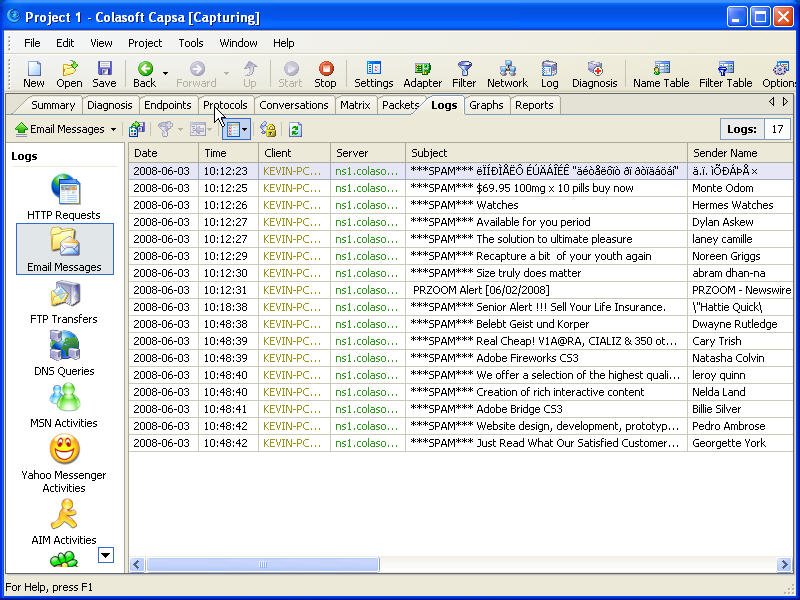
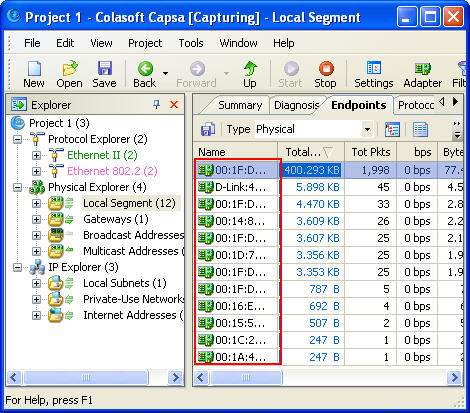
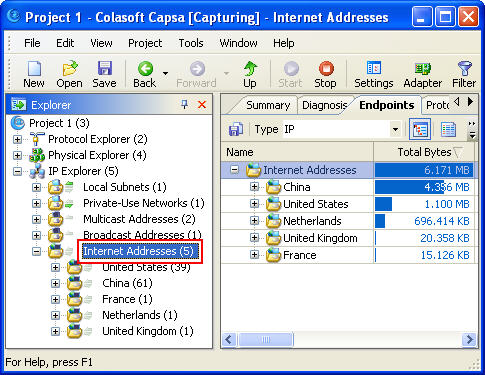
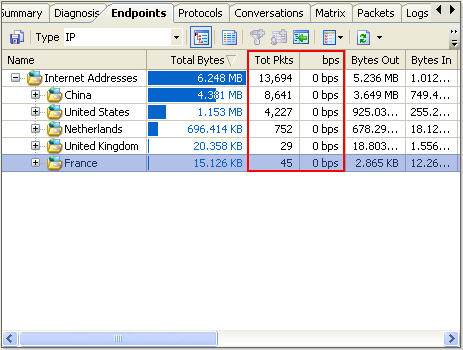
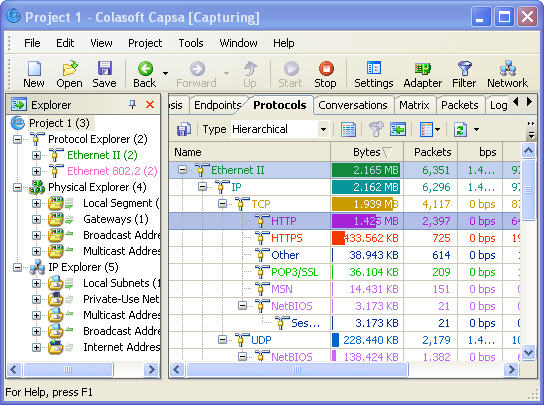
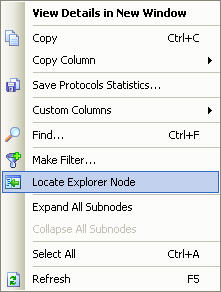
Why Protocol Analyzing Important?Since all network communications are based on protocols and different protocols indicates varieties of network behaviours, by analyzing protocols using a Packet Sniffer, we get to know what network applications are used on the network and what network behaviour is taken against your network. You may check out our protocols database to get an explanation of each protocol.
Analyze Protocols With Packet SnifferA
Packet Sniffer is an important part of the
Network Manager's toolkit. Traditionally sniffers are useful for troubleshooting networks and SNMP tools are better for trending and service management. The combination of an SNMP based Performance Manager and a well-featured
Packet Sniffer will allow you to perform many of the fundamental tasks required for successful network management.
Packet Sniffers, often called "packet sniffers" after Network Associates market leading Sniffer product, capture packets and decode them into their component parts. It's fairly obvious how sniffers can be used to troubleshooting network problems. Once a problem is detected packets are captured and analyzed and the details of the communication can be worked out. But sniffers can do more than this and, in fact, turn out to be surprisingly useful in many aspects of network management.
Unexpected Traffic The obvious thing to do is monitor the network for unexpected traffic. Most network managers know the types of application that they expect to see and can point out anything unusual. If anything unexpected is spotted then a capture of some of the traffic is usually sufficient to pinpoint the machines involved.
Unnecessary Traffic Many machines to be set by default to run protocols that may not be required.
For Example: Many printers broadcast using Novell's IPX protocol. It is fine if you are using NetWare, but not always necessary. It's good housekeeping to remove any protocols that you do not need. You may be concerned about how your users are using the available bandwidth. A good sniffer will allow you to filter specific types of traffic, so that you can keep an eye on any traffic that may cause you a problem.
Unauthorized Program Use It is useful to check the specific port numbers for services on your Servers. Most common services operate on defined port numbers, a packet capture on a Server will soon reveal what services are running. You can disable any services that you do not need. This has two benefits, one, it avoids unnecessary traffic on the network, and second it means that no unauthorized user can take advantage of that service. If anyone is using a service a packet capture will show you the address. Most sniffers allow filtering on specified port numbers so it is possible to monitor continuously for specified port numbers.
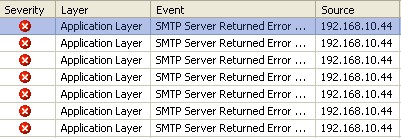
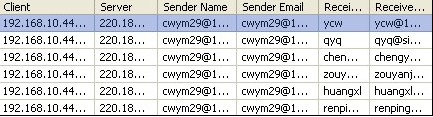
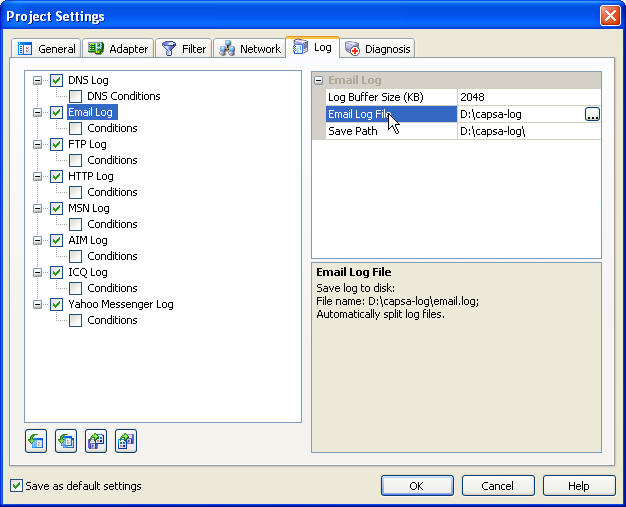
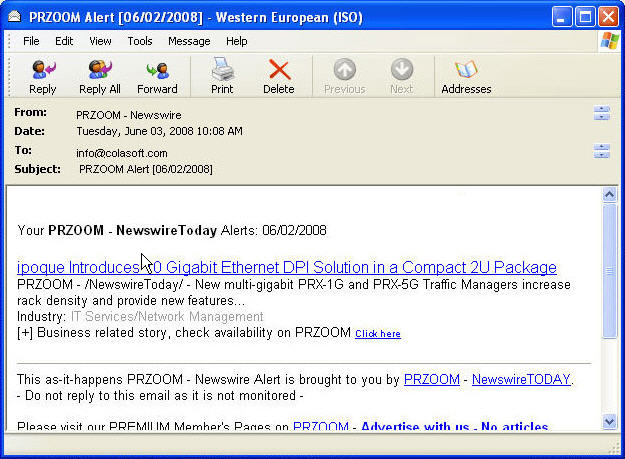
Email Problems Email systems typically use standard port numbers, 25 for SMTP, 143 for IMAP, 110 for POP3. Setting filters for these ports will usually help to discover the cause of problems with email.
Virus Detection and Control Antivirus software manufacturers offer updates services. Armed with the information on new threats it is often possible to build suitable filters to detect viruses. For example many sniffers allow you to specify a text pattern, so a virus contained in a message containing a known text string could be detected. Analysis of the capture will show the source and destination of the packets.
Firewalls Firewalls need to be checked for outgoing and incoming traffic. You will have to define a set of filters for traffic in both directions. Should the firewall begin to let unauthorized traffic through you need to be able to detect it.
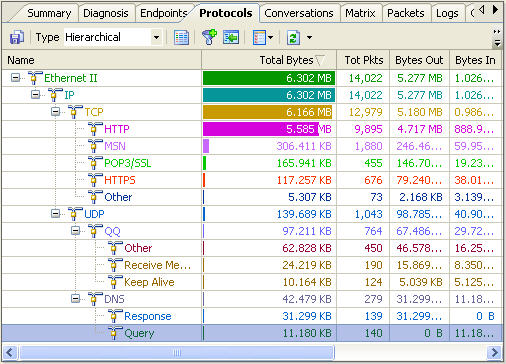
For Example: TCP is a Reliable connection oriented Protocol. Common Applications of TCP are Email and File Transfer. TCP is optimized for accurate delivery rather than timely delivery, and therefore, TCP sometimes incurs relatively long delays (in the order of seconds) while waiting for out-of-order messages or retransmissions of lost messages. So TCP analysis is required with Colasoft Packet Sniffer for finding delays.
UDP is a Reliable Connectionless Protocol. Common Applications of UDP are DNS, VOIP, IPTV and FTP.Sometimes Packet loss will happen during transmission and no help for this. Using Colasoft Packet Sniffer we can find the loss
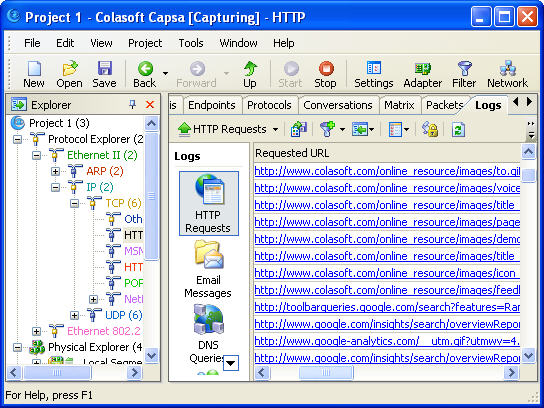
HTTP is a request/response standard of a client and a server. A client is the end-user; the server is the web site. The client making a HTTP request—using a web browser, spider or other end-user tool—is referred to as the
user agent. The responding server—which stores or creates
resources such as HTML files and images—is called the
origin server. Certain design features of HTTP interact badly with TCP, causing problems with performance and with server scalability. Latency problems are caused by opening a single connection per request, through connection setup and slow-start costs. Scalability problems are caused by TCP requiring a server to maintain state for all recently closed connections. Colasoft Packet Sniffer is used to detection such problems.